Setting up the SonicWALL firewall for using SSL VPN is pretty simple, even when it comes to utilizing Windows Domain Accounts via RADIUS authentication. The following article is a step by step guide how to configure the firewall and Windows Servers to accomplish this.
Configure Windows Server for RADIUS authentication
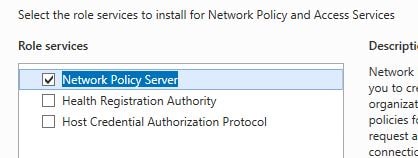
Step 1 – Install NPS
Add the Network Policy Server role on your Windows server if it’s not yet already installed.
Step 2 – Configure NPS
Add a RADIUS client to NPS using the LAN IP address of the SonicWALL firewall, and create an applicable Shared Secret password.

Step 3 – Create VPN Global Group
In Active Directory, create a global group called “SSL-VPN Access” and add the applicable users to this group that will require remote VPN access.

This Wisconsin manufacturer needed to modernize its IT infrastructure to support rapid business growth.
Discover what they didStep 4 – Create New Network Policy in NPS
Create a new Network Policy and call the policy, “SonicWALL SSL VPN“. Add the condition Windows Groups, and click ADD. Specific the “SSL-VPN Access” global group you previously created in Active Directory. Make sure the Access Granted radio button is selected for the Permission properties, and use the default selections for Authentication Methods, Configuration Constraints, and Configuration Settings, then select Finish in the Add Network Policy wizard.
Configure SonicWALL for RADIUS authentication
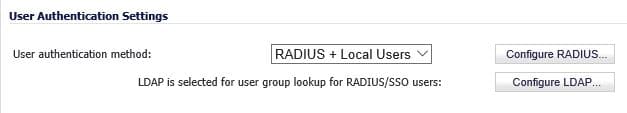
Step 1 – Change User Authentication mode
Go to Users -> Settings and change User Authentication method from “Local Users” to “RADIUS + Local Users” (this allows you to use either local user accounts created in the SonicWALL OR use Active Directory based user accounts during authentication. I suggest keeping a local user setup in the event the RADIUS server(s) go down unexpectedly.)
Step 2 – Configure RADIUS settings
Select the Configure RADIUS button and change the settings on each tab to the following:
Tab – Settings
Setup the Primary and Secondary (optional) RADIUS server and previously defined Shared Secret password.

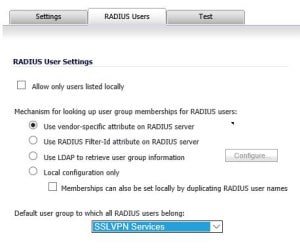
Tab – RADIUS Users
Make sure to change the Default User Group for all RADIUS users to belong to “SSLVPN Services”
Tab – Test
Specify a user account that you added as a member to the previously created “SSL-VPN Access” global group, enter the applicable user password. Change the radio button to MSCHAP or MSCHAPv2 and click Test. You should receive a response of, “Radius Client Authentication Succeeded”.
Step 3 – Save Settings
Click Accept at the bottom of the page
Configure Local Group Access
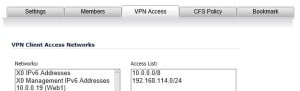
Step 1 – Edit Group Properties
Go to Users -> Local Groups and edit the properties of the SSLVPN Services local group. On the VPN Access tab, make sure you add your internal networks (address objects) that users would need to access, otherwise you won’t be able to access any internal networks even if you’ve successfully connected to the VPN.
Configure SSL VPN settings
Step 1 – Configure Server Settings
Go to SSL VPN -> Server Settings and enable the WAN interface at port 443 (the round icon should turn green). Please note — you will have to make sure the SonicWALL’s administration webpage is set to something other than 443 for this to work (configured under System -> Administration -> HTTPS Port). I typically recommend changing the administration port to 444 or 4433 so 443 is available and can be used for SSL VPN functionality.

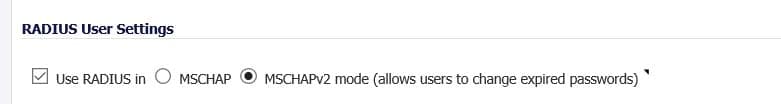
Step 2 – RADIUS User Settings
On the same SSL VPN -> Server Settings page, Enable the “Use RADIUS in” checkbox and select the “MSCHAPv2 mode” radio button.
Click on the Accept button to save the settings.
Step 3 – Configure Client Settings
(note particular these settings seem to change with every release of the SonicWALL OS unfortunately…)
Go to SSL VPN -> Client Settings and click on the configuration/edit button. Mouse-over the Address for IPv4 column, and note the address range selected for SSL VPN IP Pool. You MAY have to adjust this range accordingly to your network scheme (this is adjusted under Network -> Address Objects).
Tab – Settings
Verify the Zone IP v4 and Network Address IV V4 information
Tab – Client Routes
Add all the applicable client routes that are necessary for VPN access. In most cases, you would end up address the necessary Address Objects for all your internal networks. (These are the same networks (address objects) that you previously defined under the SSLVPN Service local group.
Tab – Client Settings (figure 8)
Verify the DNS Server 1 and DNS Server 2 are properly specified. Take note of the setting “User Name and Password Caching” and adjust accordingly to your security policy! Enabling “Create Client Connection Profile” will allow the SonicWALL NetExtender client to save the profile (recommended).

That’s all you need in order to setup SonicWALL SSL VPN to use with a Windows RADIUS server and make use of Active Directory for the VPN login authentication! Should take about 15 minutes or so to setup start to finish…




