If you’re like most firewall administrators, you dislike the idea of opening up port 25, 465, and 587 for outbound traffic to the -entire- internet. Doing so can result in your organization’s public IP address getting blacklisted in a hurry if any of your internal devices get infected with malware, or viruses, that start sending out massive amounts of email spam from bots. In this article, we walk you through the steps to find the Gmail IP address ranges you need.
In general, security conscious firewall administrators will limit outbound port 25, 465, and 587 traffic through the firewall to specific destinations and sometimes from specific internal sources as well – such as an SMTP relay server. When using a full (or fat) email client such as Outlook, Mail, or eM Client (instead of using web-based email) for sending and receiving email with Gmail based email accounts, it is important to know all the public Gmail IP address ranges used by Google for SMTP. Getting these public Gmail IP address ranges can easily be accomplished using the DIG command.
Setting your firewall up to limit outbound SMTP to ONLY those specific public IP address ranges, can help limit your exposure, and allows the email client to work properly without random error messages stating it couldn’t properly send outbound mail. While Google tends to publish this information in various tech notes on their webpages, the information on those webpages is usually outdated and not completely up to date. Using the DIG command to determine the IP address ranges used by Gmail can help to better determine which IP address ranges to allow through your firewall.
So how can someone determine the public Gmail IP address ranges that Google seems to change from time to time? The steps below utilizing the DIG command will provide you this information.

This Wisconsin manufacturer needed to modernize its IT infrastructure to support rapid business growth.
Discover what they did(Note – if you don’t have DIG on your computer, there are numerous online tools that support DIG commands that can be utilized with ease, such as https://www.digwebinterface.com)
Steps to find the Gmail IP address ranges
The first step is to issue a DIG command to get the SPF record used for gmail.com (TXT record)
You can do this with the following command:
DIG gmail.com txt(or you can use an online tool as shown in the following picture)
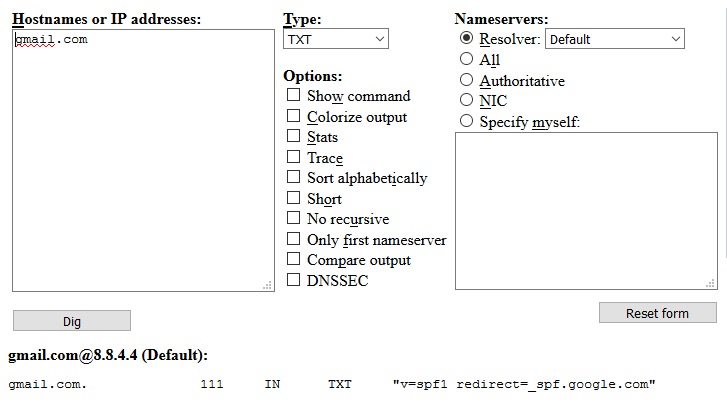
We can see here that the results come back with the FQDN of _spf.google.com. We need to issue another DIG command against that.
DIG _spf.google.com txtThe results come back here showing 3 different FQDNs:
_spf.google.com. 283 IN TXT “v=spf1 include:_netblocks.google.com include:_netblocks2.google.com include:_netblocks3.google.com ~all”We will then need to DIG each of the following netblocks that were reported back from the DIG command:
- google.com
- google.com
- google.com
This will provide ALL the current address ranges that can be used for sending SMTP mail traffic to Google.
DIG _netblocks.google.com txt_netblocks.google.com. 3599 IN TXT “v=spf1 ip4:64.18.0.0/20 ip4:64.233.160.0/19 ip4:66.102.0.0/20 ip4:66.249.80.0/20 ip4:72.14.192.0/18 ip4:74.125.0.0/16 ip4:108.177.8.0/21 ip4:173.194.0.0/16 ip4:207.126.144.0/20 ip4:209.85.128.0/17 ip4:216.58.192.0/19 ip4:216.239.32.0/19 ~all”DIG _netblocks2.google.com txt_netblocks2.google.com. 2470 IN TXT “v=spf1 ip6:2001:4860:4000::/36 ip6:2404:6800:4000::/36 ip6:2607:f8b0:4000::/36 ip6:2800:3f0:4000::/36 ip6:2a00:1450:4000::/36 ip6:2c0f:fb50:4000::/36 ~all”DIG _netblocks3.google.com txt_netblocks3.google.com. 2659 IN TXT “v=spf1 ip4:172.217.0.0/19 ip4:108.177.96.0/19 ~all”The results
Based on what the DIG command reports back, as of September 2017 the public Gmail IP address ranges currently include:
64.18.0.0/20
64.233.160.0/19
66.102.0.0/20
66.249.80.0/20
72.14.192.0/18
74.125.0.0/16
108.177.8.0/21
108.177.96.0/19
172.217.0.0/19
173.194.0.0/16
207.126.144.0/20
209.85.128.0/17
216.58.192.0/19
216.239.32.0/19
Instead of having an outbound firewall rule that allows port 25, 465, and 587 traffic to ALL external IP addresses, you can limit your firewall rule to allowing outbound traffic to ONLY those Google based IP addresses.
Yes, that’s a lot of different address ranges, and it’s likely that these Gmail IP address ranges will change over time and in the future, but knowing these IP address ranges allows you to more safely setup an outbound rule on your firewall that allows port 25, 465, and 587 traffic to those specific ranges of external Gmail public IP addresses so your mail clients (Outlook, Mail, eM Client, etc.) can send outbound email without getting random or intermittent errors.




